GbJade Networks
ReSieve Help File
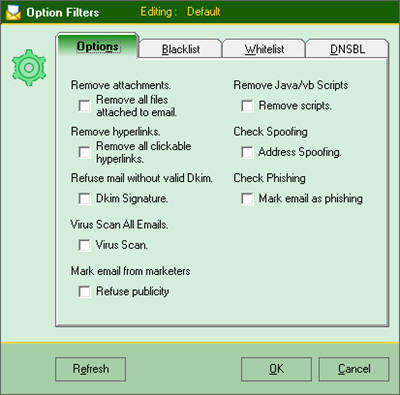
8 options are avialable at the time of writing. More is to come. Follow us on
GbJade.com We accept comments and sujestions.
By selecting any of these options, RSF will modify the email file before
sending it to the client software. For your convenience, RSF will keep a copy of
the original email, untouched/unmodified in case you wish to view it in its
oringal state. We have created two tools for you. If the email is still in the
storage directory, you need to use the "Search and Rescue" module. To get access
to this module click in the menu config/Search and Rescue. If the wanted email
has been recieved more than the number of days to keep in starage, you will have
to use the "Backup Archive" module.
| Note : By using the tools mentioned above, you have to make sure
your looking into the right group name. Otherwise the email will not be
found. |
By default, RSF has not chosen any options for you. Wanted options varies too
much from one company to an other. There are 3 well known ways that a network
can be hacked.
1: Badly configured servers and workstations.
2: The
hacker is getting help from inside your company or the hacker is your employee.
3: This is the most frequent way of penitrating your network. Somthing
malisious has been inserted in a file attached to an email. Beware of macros
programmed in Office files like .doc(Microsoft Word), .xls(Microsoft Excel).
Some files like .jpg(picture) has been reported to be dangerous and .pdf files
too. Microsoft Office is not the only software that can create macros. There are
many office work software on internet that can do the same.
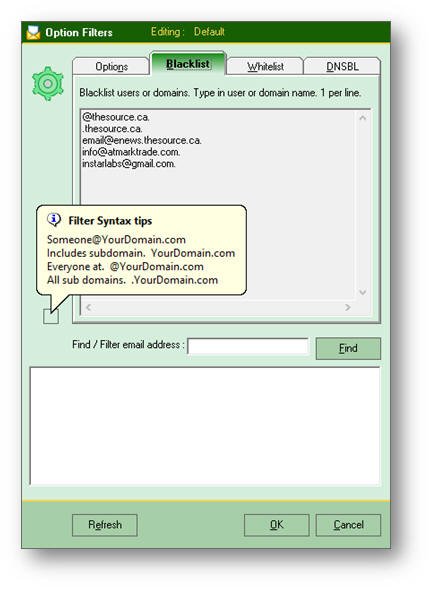
Black listing
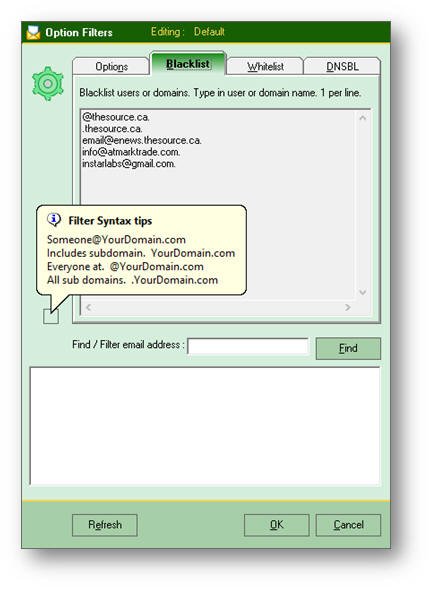
2 technics are offered. The local blacklist database, as shown below, the one
that you have controle on and the DNSBL. These databases are on remote servers
accessible from the internet and which you have no controle.
The syntax is quite simple for this module. Examples are shown below.
| Match Type |
Examples |
|
john@YourDomain.com
|
Matches same address only. john@YourDomain.com
|
|
YourDomain.com
|
Matches all addresses coming form
YourDomain.com including sub-domains.
john@YourDomain.com
john@Sub.YourDomain.com , etc.
|
|
@YourDomain.com
|
Matches all addresses coming in at
YourDomain.com but excludes all sub-domains.
Matches
john@YourDomain.com but does not match john@Sub.YourDomain.com
|
|
.YourDomain.com
|
Matches all addresses of sub-domains of
YourDomain.com
Does not match john@YourDomain.com but matches
john@Sub.YourDomain.com
|
You don't need to memorize these technics. GbJade has inserted a square box in
which you can put your mouse over. The 3 technics will be shown to you. Look at
the left hand side of the windows.
| Note : Emails tagged as blacklisted are not deleted. Emails will be
tagged as such before sending it to the email client. "Sender
blacklisted from local database" tag will be inserted at the begging of
the maessage. A copy of these emails are kept on RSF device for your
conveniance. |
Whitelisting has the same parts and syntax as the blacklisting. Pease proceed in
the same way.
To find email addresses and/or domain names, simply enter a clue word for RSF to
search and press enter, or click the "Find" button.
The results will be shown
in the bottom window. Simply double click on the desired line. The same text
line will appear in the blacklist window. Format this line to reflect the
desired email address or domain name.
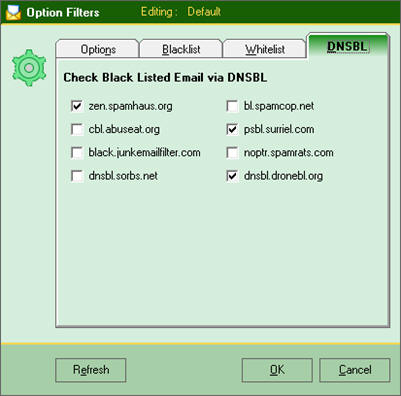
DNSBL filtering
To verifying
if the domain name
and/or the IP address is listed in the internet black
list database.
Select which database you wish to
compare the sender's domain/IP address.
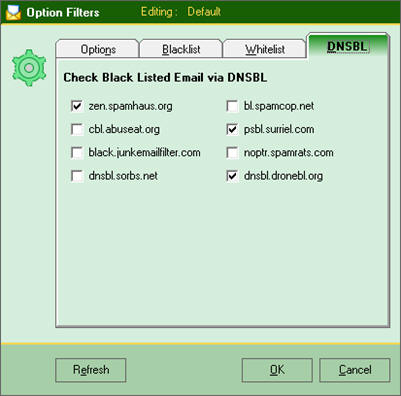
| Note:
the more database you select the slower your RSF
will become. This is not related to the internal
resource of RSF. It's related to your internet
connection provided by your ISP and the speed the
remote database. If remote database server(DNSBL) is
overwhelmed or off line, RSF will wait till the answer is given or
disconnect from the remote database after 60 seconds. |
|